Tech News
The outbreak of WannaCrry made a huge impact globally, the major security agencies and users have to patch or limit 445 port and etc in order to strengthen the old version of Windows system protection.
However, this virus variant is the easiest to ignore the way to accelerate the penetration of long-term to Windows virus immune a.k.a Linux has also been infected.
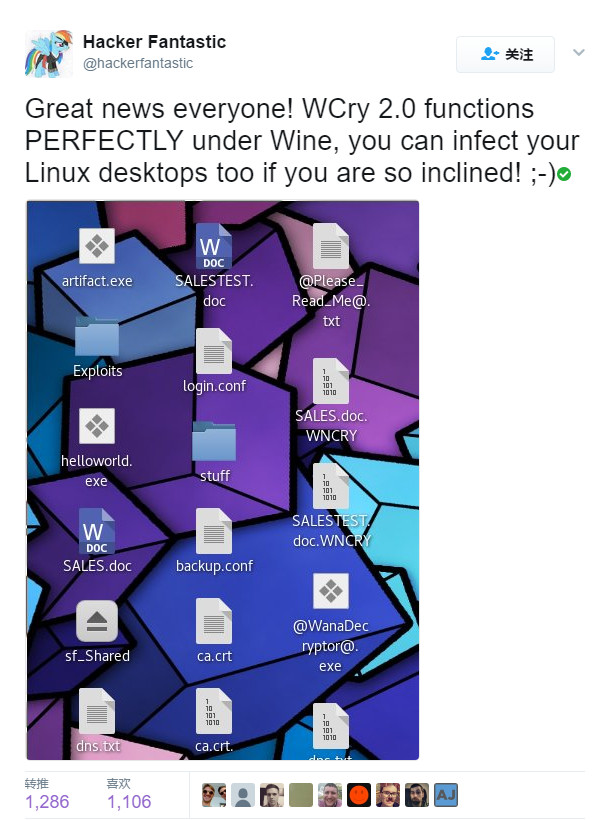
According to Hacker Fantastic, co-founder of Myhackerhouse (Network Security Company) they have tested and found that the latest variant of the bitcoin ransomware virus WannaCry2.0 will infect your Linux machines that run under Wine. We want to remind Wine’s user that the compatible layer of Linux is highly vigilant.
Wine
(The recursive abbreviation for “Wine Is Not an Emulator”) it’s a compatible layer that can run Windows applications on a variety of POSIX-compliant operating systems such as Linux, Mac OSX, and BSD. In short, Wine can work in most Unix / Linux versions, you can run many Windows programs, Wine also supports Windows executable (.exe).
Source from Hacker Fantastic.
Latest Update: From askubuntu.com
On May 14, 2017 Red Hat Linux said they are not affected by “Wanna Cry” ransomware. This might mislead Ubuntu users along with Red Hat, CentOS, ArchLinux and Fedora users. Red Hat supports wine which answers below confirm can be effected. Hence, Ubuntu and other Linux distro users googling this issue might mislead by the Red Hat Linux Support answer
Red Hat supports wine. Hence, Ubuntu and other Linux distro users googling this issue might mislead by the Red Hat Linux Support answer here.
1. How does it spread?
Answers: Email.
2 friends were affected. They send the email to me to test under a supervised environment, so you would basically need to open the email, download the attachment and run it. After the initial contamination, it will systematically check the network to see who else are affected.
2. Can I get affected by using Wine?
Answer: Yes.
Since Wine emulates almost every behavior of the Windows environment. The worm can actually find a loophole to get through by itself. Furthermore, it depends on the access of wine granted in your Linux machine. Probably some or all of your home folder will get infected (Did not fully test this. See answer 4 below).
Although, I see a lot of roadblocks on how the worm behave, encrypt a non-NTFS/FAT/files and what non-super admin permission would it need to perform the action, In short, the action doesn’t need full access to do so. In any case, it’s better to handle your important folder with extra caution.
3. How can I test the behavior of this once I get an email that has it?
My initial test which involved 4 VirtualBox containers on the same network ended in 3 days. Basically, on day 0, I contaminated on purpose of the first Windows 10 system.
After 3 days, all 4 were affected and encrypted with the “Whoops” message about the encryption.
Surprisingly, Ubuntu was never affected, even after creating a shared folder for all 4 guests on the Ubuntu desktop (Outside of Virtualbox). The folder and the files in it were never affected. Now, I have my doubts on Wine and how does this can propagate it.
4. Did I test it on Wine?
Answer: Yes, I did test it on Wine. Resulting my desktop and music folder were doomed. However, It did not affect the folder that I had in another drive, maybe because it was not mounted during that time.
I run wine as sudo and it affected the Desktop and Music folder. For your Information, I Am using Ubuntu 17.04 64-Bit, partitions are Ext4 and I did not install or configure any other security measures to the machine.



Leave a Reply
Want to join the discussion?Feel free to contribute!